Feature Flags and Compliance: How Audit Trails Protect Regulated Teams
In a regulated environment, a feature that ships without a paper trail isn't a release — it's a liability.
Healthcare, finance, and payments teams operate under strict frameworks: SOC 2, HIPAA, PCI-DSS. Every change to production must be traceable. Auditors want to know what changed, when it changed, who authorised it, and how quickly it could be reversed if something went wrong.
Traditional deployments make this hard. A git merge tells you when code landed in the repo — it doesn't tell you when the feature went live to users, which users were affected, who approved the rollout, or how it was turned off. That gap between "deployed" and "enabled" is exactly where compliance risk lives.
The Problem With Deployment-Level Traceability
When a deployment is your release event, your audit trail is a build log. It records commits and pipeline runs — not intent. There's no structured record of who decided to expose a feature to users, what criteria gated it, or whether a human approved the change before it affected real accounts.
That makes incident response slower too. When something breaks at 3am, "what changed?" becomes an archaeology exercise across four systems. The answer should be instant.
Feature Flags Create a Feature-Level Audit Record
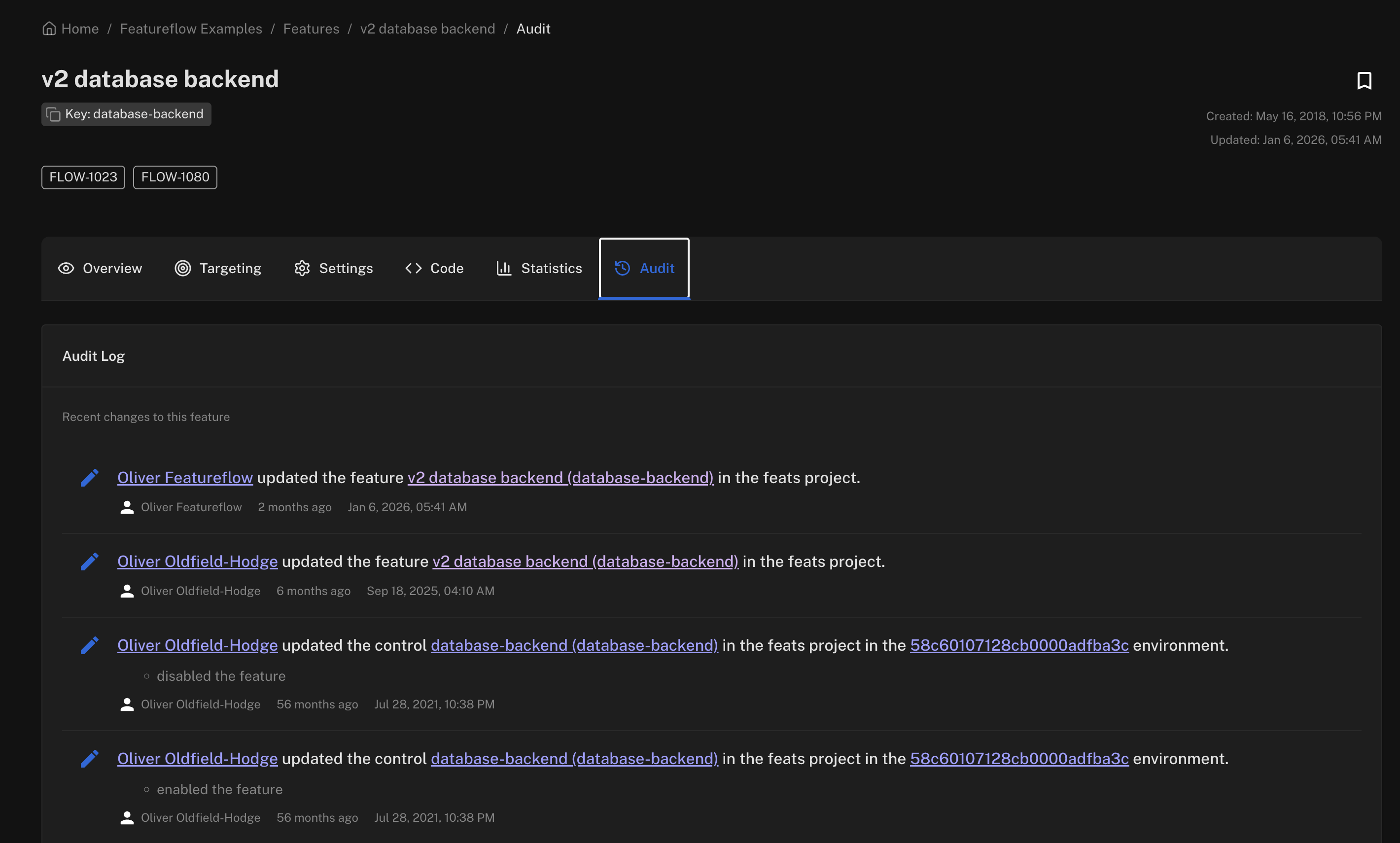
Feature flags shift your release event from the pipeline to the flag evaluation. That shift creates a natural audit log:
- Who created or modified the flag — linked to an authenticated user or service account.
- When the flag was turned on or off — timestamped, immutable.
- Which users were in scope — via targeting rules (user IDs, account tiers, percentage rollouts).
- How it was reversed — the flag history shows every state transition.
This is the kind of structured evidence auditors actually ask for. Not a wall of git commits — a clear timeline of intent and action at the feature level.
Controlled Rollout as a Compliance Control
Flags also let you enforce access controls at the feature level, not just the deployment level. Rolling out a new payment flow only to accounts in a specific region, or gating a data-sensitive feature behind an explicit user attribute, is a compliance control in itself.
Here's what that looks like with the Featureflow JavaScript SDK:
import featureflow from 'featureflow-client';
const user = {
key: account.id,
attributes: {
tier: account.tier, // e.g. 'enterprise'
region: account.region, // e.g. 'EU'
},
};
const client = featureflow.init(API_KEY, user);
if (client.evaluate('new-payment-module').value() === 'on') {
// Only rendered for users matching your targeting rules.
// The flag evaluation is logged — traceable, reversible.
renderNewPaymentFlow();
}Targeting rules in Featureflow are declarative and version-controlled — you can show exactly what criteria were active at any point in time. That's a meaningful difference from ad-hoc conditional logic scattered across your codebase.
Instant Rollback Is Also a Compliance Story
Regulators don't just care whether changes are traceable — they care whether you can respond fast when something goes wrong. Mean time to recover (MTTR) is a metric that appears in SOC 2 audits for a reason.
A flag kill switch reduces MTTR from "redeploy + hotfix" to "flip a toggle." No pipeline run, no war room, no rollback PR. The flag change is logged, timestamped, and tied to an authenticated actor. That's exactly the kind of documented response process that auditors want to see.
Compliance teams in regulated industries often push back on speed — worried that continuous delivery means continuous risk. Feature flags reframe the conversation. You're not deploying to production recklessly; you're deploying dark and enabling deliberately, with full traceability at every step.
👉 See how Featureflow handles targeting, rollouts, and flag history at featureflow.com.
#FeatureFlags#Compliance#AuditTrails#ContinuousDelivery#DevOps
Traceable releases start here
Start free with Featureflow — feature-level audit trails, targeting rules, and instant kill switches out of the box.
Start Now (Free)Related Articles
Feature Flags vs Entitlements: When to Use Which (and When You Need Both)
Feature flags release code safely. Entitlements decide who's paid for what. Collapse them into one toggle system and you'll end up with billing tied to deploys, or risky releases hidden in your pricing layer.
Testing Code That Has Feature Flags: Strategies That Don't Explode Your Test Matrix
Add ten boolean flags and you have 1,024 versions of your app — in theory. Here's how to keep your test suite tractable: stub the SDK, pin variants per test, default to safe, and clean up alongside the flag.
Feature Flags and the Strangler Fig: Refactor Legacy Code Without the Big-Bang Rewrite
Big-bang rewrites kill teams. The strangler fig pattern with feature flags lets you replace legacy code one slice at a time — shadow-testing, ramping traffic, and keeping a kill switch the whole way.